Contents
2.10.1 Mobile Connection Methods
Cellular Networks
- Available in most urban and suburban areas
- 1 single tower can cover distances of up to 20 miles
- Rated according to the generation of services
WIFI Networks
These cover shorter distances with greater bandwidth.
Satellite Communications
This works almost anywhere but is expensive and slow.
Near File Communications (NFC)
This covers distances measures in centimetres using electromagnetic induction. This can be used for short, transnational; communication such as mobile payments.
Bluetooth
This works over a longer range than NFC, up to 30 feet. This is often used for the communication between devices such as headsets, speakers, or car audio systems.
ANT Networks
These allow connections between sensors and controllers. It is most commonly used for fitness devices. It is a proprietary system by ANT.
USB Connections
This often allows wired connectivity for mobile devices. EG: connecting a mobile device to a desktop to use the desktops network connection, or Vice versa, tethering the desktop or laptop from the mobile device.
2.10.2 Mobile Device Security
Mobile devices are a gateway to sensitive information and therefore need strong security controls.
Access Control Mechanisms
The most common of these is a passcode. You should not use 4 digit pins, they are not very secure.
Bio-metric authentication offers a convenient secure alternative.
Device Encryption
Both Apple and Android devices encrypt the data on your phone when you use a passcode.
Remote Wiping Technology
This can be used to wipe your phone if it is lost or stolen. But it needs to be connected to a network.
Auto-Lock
Lock devices automatically after a short period of inactivity.
Securing Mobile Device Apps
Many apps use sensitive data and therefore must have strong security controls.
- Implement policy to restrict the types of apps that can be installed on the device
- Authentication: any app the has access to sensitive data should have authentication with strong security. Where possible use central authentication. You can also use Context-Aware Authentication. This changes authentication requirements based upon a real-time assessment of the users request and operating environment. These factors include: physical location, type of request, the device the user is using etc…
- Encrypt Sensitive Information: data at rest of the device and in transit should be encrypted
- Geotagging: mobile devices now incorporate GPS to allow the device to pinpoint its location on the planet.
Mobile Security Enforcement
The following are some things to lookout for when managing the security of mobile devices.
- Third Party App Stores: These may contain some unsafe code
- Jailbreaking phones creates added security risks
- Mobile devices must be patched regularly
- Restrict device feature use:
– Cameras – if it’s a sensitive site
– Messaging
– External media
– Microphone
– USB on the go
– GPS tagging (this could disclose users location in a photo)
– Device tethering
– Mobile payments technology
2.10.3 Mobile Device Management (MDM)
MDM’s are a way of centrally managing the security on many mobile devices simultaneously. There are many different vendors offering MDM solutions.
MDM Features
- Create policies for devices
- Perform device and configuration management
- Prevent users from modifying security settings
- Control data stored on devices (revoking user access or wiping devices)
- Manage applications (Blacklist or whitelist apps)
- Storage Segmentation (Containerisation). Some MDM’s allow you to set this up so work and personal data are stored separately on the phone
Containerisation
This is a MDM technique that facilitates the use of devices for personal and business purposes, and keeping the data separate. It provides a secure encrypted portion of the device for business use which normally runs inside of a mobile app. The information in this container cannot be accessed by other apps.
2.10.4 Mobile Device Tracking
Loss of mobile devices introduces confidentiality and financial risks, therefore it is imperative that you can track mobile devices. With the rising cost of mobile devices you also don’t want to lost any as that can quickly become very expensive.
Asset Tracking Software
This software should manage the entire lifecyle of the device.
- Device request
- Ordering and receiving
- Initial configuration
- Device assignment
- Device decommissioning
GPS
Geolocation allows the real-time and historical location of GPS enabled devices.
Geofencing allows you to graph out a geographical area and then create alerts for when a device leaves this defined area
GPS use limits:
- Limited access to GPS data
- Ability for monitored individual to disable tracking
- Automated disabling outside of work hours
- Clear disclosure of use
2.10.5 BYOD (Bring Your Own Device)
Gartner predicts that in the next 2 years half of employers will require employees to BYOD to work.
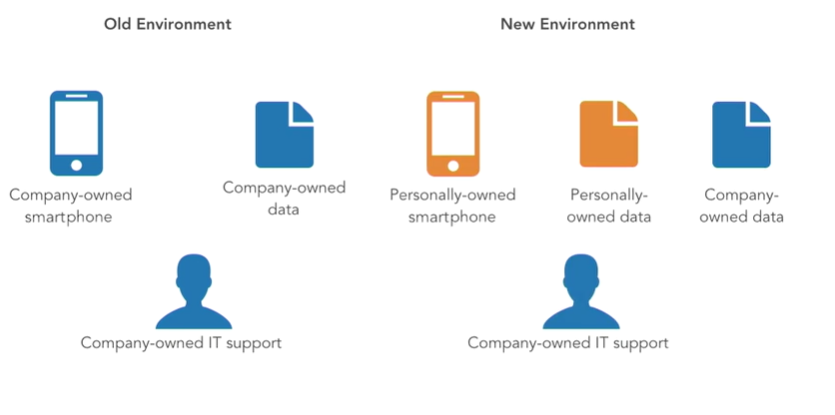
BYOD Policy
If using BYOD you need to have a firm policy:
- Who may bring devices to the workplace?
- What devices may they bring?
- How will the security of those devices be managed?
- Will the acceptable use policy be different?
- Users should understand monitoring of their device
- What level of support can IT give to these devices?
Technical Implications of BYOD on IT Infrastructure
- No standard of hardware, apps, OS etc…
- Mobile device management?
- Patching and AV management
- Camera use
- Forensic procedures: what can you do in the case of a BYOD is compromised? Will IT perform forensic analysis on personally owned devices?
BYOD Onboarding/Offboarding
Onboarding: Ensure the device meets security requirements and is safely configured. Give user policy on what data can be saved on the device.
Offboarding: Remove all corporate information from the personally owned device.
2.10.6 Mobile Deployment Models
While the BYOD approach works for some organisations, others seek more control over the devices or don’t want employees to bear the burden of purchasing and maintaining their own mobile devices. For this reason, some alternative strategies have cropped up that supplement BYOD and the traditional company owned device model.
CYOD (Choose Your Own Device)
This recognises that different employees have different requirements when it comes to devices. Some people like Apple over Android etc…Some organisations give the employees an allowance to buy their own devices. But it is more common for the organisation to give the employee a menu from which they can choose their device.
COPE (Company Owned, Personally Enabled)
This allows users to use corporate devices for personal use. This avoids the issue of users bringing their personal devices to work and the possibility of them putting sensitive corporate data on these devices.
Virtual Desktop Infrastructure (VDI)
This is becoming increasing popular. This runs desktops in the cloud or data centre. The employee can connect to these desktops from their personal device and work. The data never leaves the organisations network.
