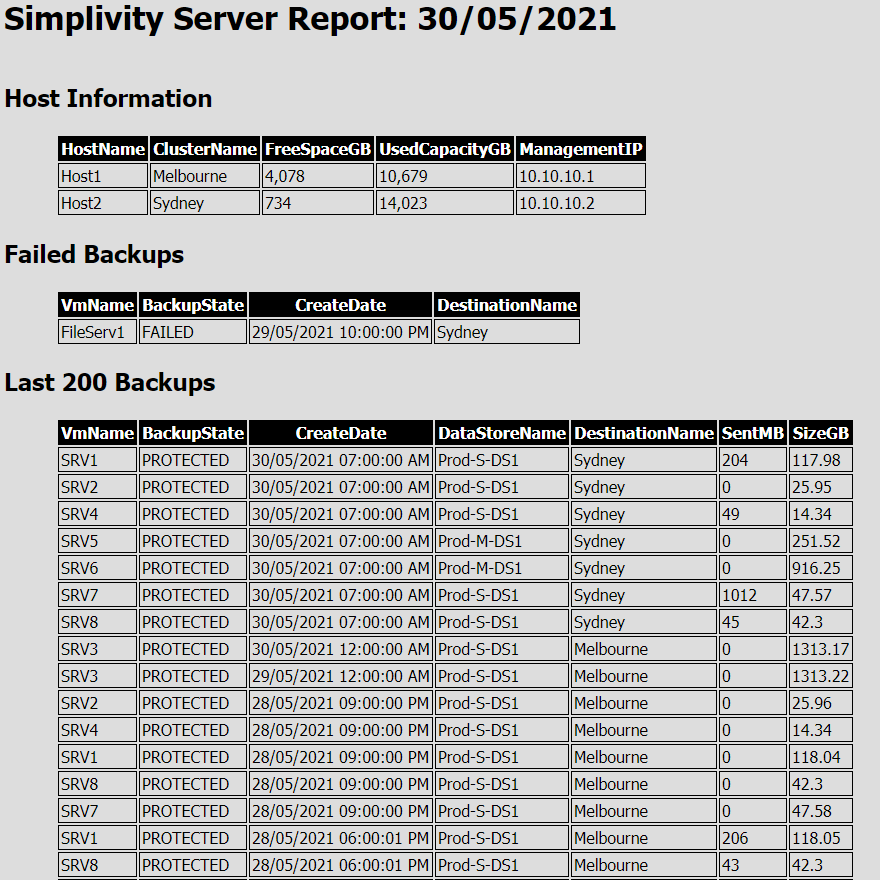
An issue with Flash in the web browser and the version of Simplivity we are running forced my hand to learn to manage the backups using PowerShell. I started managing the backups through the Simplivity CLI but then discovered there was an PowerShell API which made life a lot easier. If you have experience using PowerShell you will find these…
AZ-104: Microsoft Azure Administrator (Study Notes)
I am currently studying for my AZ-104: Microsoft Azure Administrator exam. I am studying the content using Scott Duffy’s course on Udemy, which I highly recommend: https://www.udemy.com/share/101WoMAEYdcl5bRn0F/ On the following posts I will be uploading some of my study notes. This keeps me honest with making sure I keep have decent notes and hopefully they will be of help to…
Managing DHCP Scopes with PowerShell
Introduction We recently restructured our whole IP addressing schema. This was a mammoth job. The management of DHCP scopes was one part of this. We had to create around 20 new DHCP scopes and create reservations for all the devices that reservations in the old scopes. I thought to myself that this is the perfect time to learn about using…
Exchange Online Migration error: “Target user already has a primary mailbox”
Issue When migrating mailboxes from Exchange On Premise to Exchange Online, it fails with the following error: Target user ‘Users Name’ already has a primary mailbox. Cause Long before we had ever thought about migrating to Exchange Online we had manually created some students in our Office 365 tenant (not using the Azure AD Connect) to give them access to…
Comptia Security+ (SY0-501) Study Notes
I am working my way through the online course “Cert Prep: CompTIA Security+” by Michael Chapple. This is available on Lynda and LinkedIn Learning. These are my study notes- Section 1 – Threats, Attacks and Vulnerabilities 1.1 Malware 1.2 Understanding Attackers 1.3 Understanding Attack Types 1.4 Application Attacks 1.5 Vulnerability Scanning and Penetration Testing 1.6 Impact of Vulnerabilities Section…
Movement Practice
“Movement is a medicine for creating change in a person’s physical, emotional, and mental states.” – Carol Welch Why? As I am no spring chicken anymore, I noticed from my training that even though I may be still in OK shape and getting a bit stronger and fitter, I am not getting sorer and not moving well. An example is…
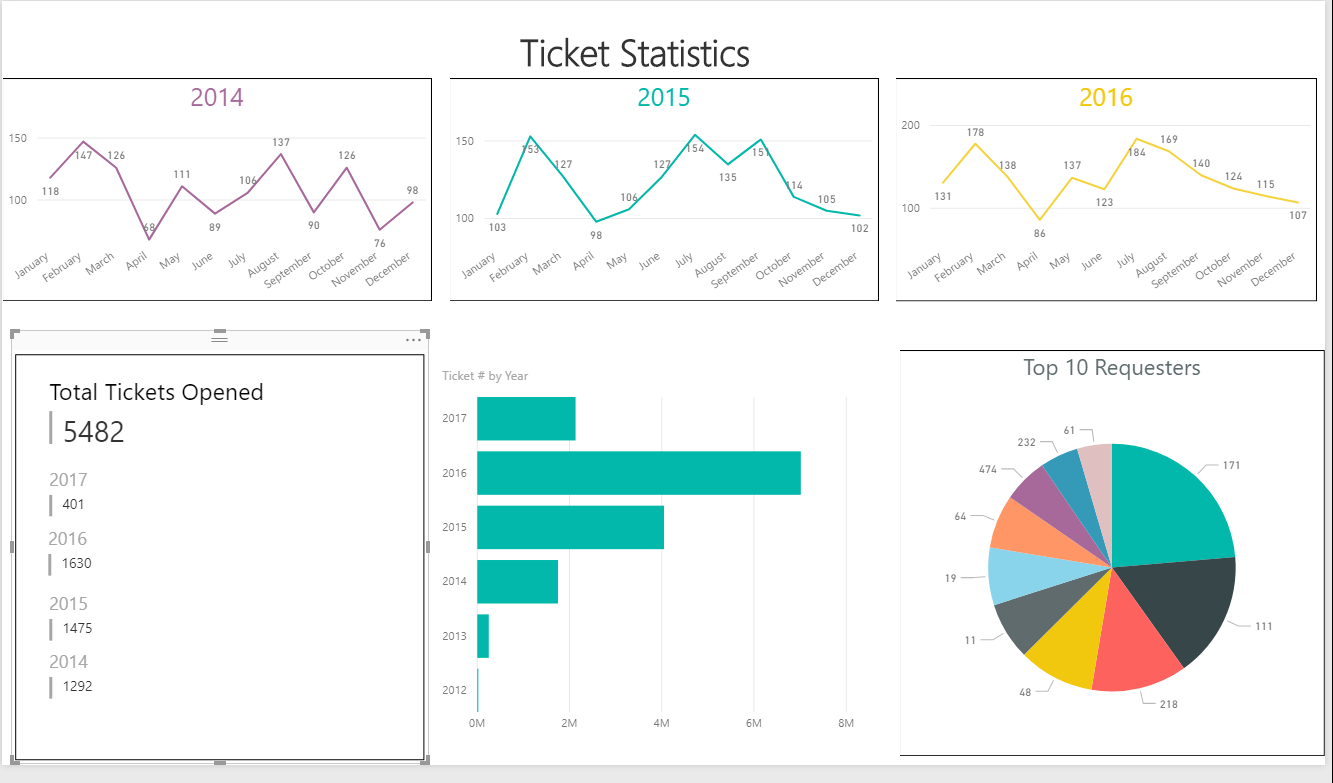
Spiceworks Reports with Power BI(with Video tutorial)
Power BI is a fantastic, and relatively easy, way of getting some great reports and analytics out of your Spiceworks database. UPDATE: I have added this video tutorial to hopefully make this clearer and easier to follow.
Spiceworks: Unassigned tickets report with PowerShell
An “Unassigned Tickets” report is very useful for making sure everyday that all tickets are being picked up and not left sitting unassigned. Spiceworks has the built in report functionality which are great, but the only issue I have with them is that you cant put report content directly in an email, it sends it as an attachment. So I…
Sentinel: Become the Agent in Charge of Your Own Protection Detail
Pat McNamara I first came across Pat McNamara on the Joe Rogan Podcast Episode #1262 in March 2019. He is an interesting cat. He spent 22 years in the US Army mostly in Special Operations units. He works out like an animal everyday. He is an expert marksman. He could kill you with his bare hands. But he also doesn’t…
How to increase confidence – Jocko Willink
Who couldn’t do with a confidence boost? Take 3 and a half minutes of your day and watch Jocko give his advice on how to increase your confidence.